方案:
https://confluence.atlassian.com/doc/confluence-security-advisory-2022-06-02-1130377146.html
Confluence存在远程代码执行漏洞预警 {#activity-name}
For Confluence 6.0.0 - Confluence 7.14.2 {#ConfluenceSecurityAdvisory20220602-ForConfluence6.0.0-Confluence7.14.2}
Data Center and Server 8.6
Confluence Security Advisory 2022-06-02
Still need help?
The Atlassian Community is here for you.
Confluence Server and Data Center - CVE-2022-26134 - Critical severity unauthenticated remote code execution vulnerability {#ConfluenceSecurityAdvisory20220602-ConfluenceServerandDataCenter-CVE-2022-26134-Criticalseverityunauthenticatedremotecodeexecutionvulnerability}
**Update:**This advisory has been updated since its original publication.
Specific updates include:
10 Jun 2022 3 PM PDT (Pacific Time, -7 hours)
- Updated the Mitigation section with steps for Confluence version 6.0.0 and above.
03 Jun 2022 4 PM PDT (Pacific Time, -7 hours)
- Updated to clarify limitation with rolling upgrades in the What You Need to Dosection.
03 Jun 2022 10 AM PDT (Pacific Time, -7 hours)
- Updated with the fixed versions
- Removed interim advice about adding a WAF rule from the What You Need to Dosection
03 Jun 2022 8 AM PDT (Pacific Time, -7 hours)
- Updating mitigation information to include replacement jar and class files
03 Jun 2022
- Clarifying the affected versions
- Adding a WAF rule to the What You Need to Do section
- Adding estimated timeframe for fixes to be available
| Summary | CVE-2022-26134 - Critical severity unauthenticated remote code execution vulnerability in Confluence Server and Data Center | | Advisory Release Date | 02 Jun 2022 1 PM PDT (Pacific Time, -7 hours) | | Affected Products | * Confluence * Confluence Server * Confluence Data Center | | Affected Versions | * All supported versions of Confluence Server and Data Center are affected. * Confluence Server and Data Center versions after 1.3.0 are affected. | | Fixed Versions | * 7.4.17 * 7.13.7 * 7.14.3 * 7.15.2 * 7.16.4 * 7.17.4 * 7.18.1 | | CVE ID(s) | CVE-2022-26134 | |-----------------------|--------------------------------------------------------------------------------------------------------------------------------------------------------|
Severity {#ConfluenceSecurityAdvisory20220602-Severity}
Atlassian rates the severity level of this vulnerability as critical , according to the scale published in our Atlassian severity levels. The scale allows us to rank the severity as critical, high, moderate or low.
This is our assessment and you should evaluate its applicability to your own IT environment.
Description {#ConfluenceSecurityAdvisory20220602-Description}
Atlassian has been made aware of current active exploitation of a critical severity unauthenticated remote code execution vulnerability in Confluence Data Center and Server. The OGNL injection vulnerability allows an unauthenticated user to execute arbitrary code on a Confluence Server or Data Center instance.
All versions of Confluence Server and Data Center prior to the fixed versions listed above are affected by this vulnerability.
This issue can be tracked here:
CONFSERVER-79016 - Remote code execution via OGNL injection in Confluence Server & Data Center - CVE-2022-26134 PUBLISHED
Atlassian Cloud sites are protected
If your Confluence site is accessed via an atlassian.net domain, it is hosted by Atlassian and is not vulnerable. Our investigations have not found any evidence of exploitation of Atlassian Cloud.
Fix {#ConfluenceSecurityAdvisory20220602-Fix}
We have taken the following steps to address this issue:
- Released versions 7.4.17, 7.13.7, 7.14.3, 7.15.2, 7.16.4, 7.17.4 and 7.18.1 which contain a fix for this issue.
What You Need to Do
Atlassian recommends that you upgrade to the latest Long Term Support release. For a full description of the latest version, see the Confluence Server and Data Center Release Notes. You can download the latest version from the download centre.
Note: If you run Confluence in a cluster, you will not be able to upgrade to the fixed versions without downtime, also known as a rolling upgrade. Follow the steps in Upgrading Confluence Data Center.
Mitigation {#ConfluenceSecurityAdvisory20220602-Mitigation}
If you are unable to upgrade Confluence immediately, then as a temporary workaround, you can mitigate the CVE-2022-26134 issue by updating the following files for the specific version of the product.
For Confluence 7.15.0 - 7.18.0 {#ConfluenceSecurityAdvisory20220602-ForConfluence7.15.0-7.18.0}
If you run Confluence in a cluster, you will need to repeat this process on each node. You don't need to shut down the whole cluster to apply this mitigation.
-
Shut down Confluence.
-
Download the following 1 file to the Confluence server:
-
Delete (or move the following JAR outside of the Confluence install directory):
<confluence-install>/confluence/WEB-INF/lib/xwork-1.0.3-atlassian-8.jar Do not leave a copy of this old JAR in the directory.
Do not leave a copy of this old JAR in the directory. -
Copy the downloaded xwork-1.0.3-atlassian-10.jar into
<confluence-install>/confluence/WEB-INF/lib/
-
Check the permissions and ownership on the new xwork-1.0.3-atlassian-10.jar file matches the existing files in the same directory.
-
Start Confluence.
Remember, If you run Confluence in a cluster, make sure you apply the above update on all of your nodes.
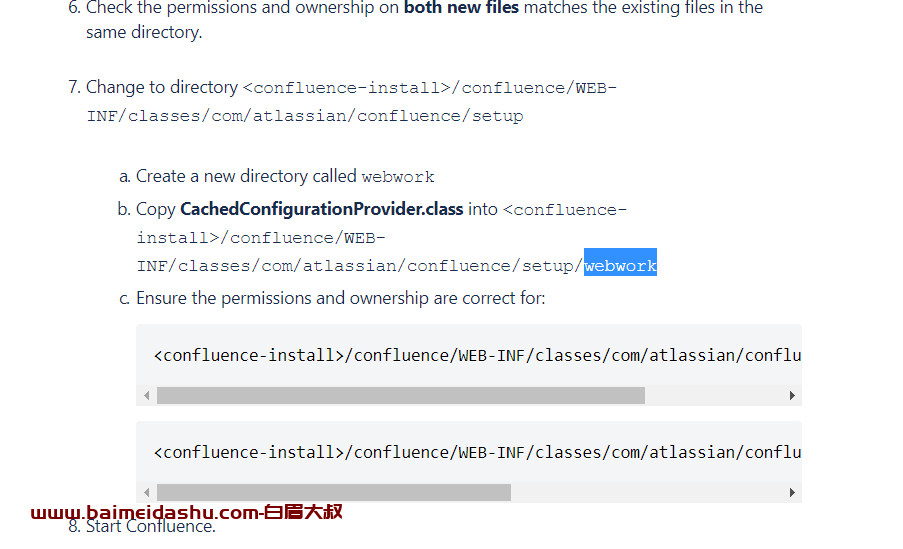
For Confluence 6.0.0 - Confluence 7.14.2 {#ConfluenceSecurityAdvisory20220602-ForConfluence6.0.0-Confluence7.14.2}
If you run Confluence in a cluster, you will need to repeat this process on each node. You don't need to shut down the whole cluster to apply this mitigation.
-
Shut down Confluence.
-
Download the following 3 files to the Confluence server:
-
Delete (or move the following JARs outside of the Confluence install directory):
<confluence-install>/confluence/WEB-INF/lib/xwork-1.0.3.6.jar <confluence-install>/confluence/WEB-INF/lib/webwork-2.1.5-atlassian-3.jar Do not leave a copy of the old JARs in the directory.
Do not leave a copy of the old JARs in the directory. -
Copy the downloaded xwork-1.0.3-atlassian-10.jar into
<confluence-install>/confluence/WEB-INF/lib/
-
Copy the downloaded webwork-2.1.5-atlassian-4.jar into
<confluence-install>/confluence/WEB-INF/lib/
-
Check the permissions and ownership on both new files matches the existing files in the same directory.
-
Change to directory
<confluence-install>/confluence/WEB-INF/classes/com/atlassian/confluence/setup
-
Create a new directory called
webwork -
Copy CachedConfigurationProvider.class into
<confluence-install>/confluence/WEB-INF/classes/com/atlassian/confluence/setup/webwork -
Ensure the permissions and ownership are correct for:
<confluence-install>/confluence/WEB-INF/classes/com/atlassian/confluence/setup/webwork<confluence-install>/confluence/WEB-INF/classes/com/atlassian/confluence/setup/webwork/CachedConfigurationProvider.class
-
-
Start Confluence.
Remember, If you run Confluence in a cluster, make sure you apply the above update on all of your nodes.
confluence docker 被黑客攻击的解决办法
confluence docker 被黑客攻击的解决办法 - 简书 (jianshu.com)
我的confluence是安装在docker上的,因为原来被黑客攻击过一次,所以使用docker部署来保证主机的安全,但是这种方法过了半年又被黑客攻击了。
黑客攻击的方式是通过confluence软件的BUG,写入主机/tmp/目录,然后一直执行定时任务,用top -c 命令你会看到后台有一堆的定时任务。然后产看端口占用 netstat -anp查看端口占用,你会发现一直有端口在被占用传输数据,比如下面的54.37.93.31:1999 ,这个IP是国外的,很明显你的服务器被当作肉机了:
【漏洞通告】Atlassian Confluence 远程代码执行漏洞(CVE-2022-26134)
【漏洞通告】Atlassian Confluence 远程代码执行漏洞(CVE-2022-26134) (aliyun.com)
 51工具盒子
51工具盒子